Latest
- All
- Barack Hussein Obama
- Conservatism
- Donald Trump
- Economy
- Education
- Election News
- Email Featured
- Featured
- flagandcross
- Government Gone Wild
- Gun Control
- Healthcare
- Hillary Clinton
- Immigration
- Iran
- Islam/Sharia Issues
- Israel
- Liberals
- Mainstream Media
- National Security
- Opinion
- Politics
- Religion 1st Amendment
- Social Issues
- Socialism
- Veterans/Military
- Worldwide Events
-
Great American RepublicApril 2, 2021
Black Teen Girls Who Murdered Uber Driver In DC Carjacking Will Receive Plea Deal (Details)
The following article, Black Teen Girls Who Murdered Uber Driver In DC Carjacking Will Receive Plea Deal (Details), was first…
Read More » -
Great American RepublicApril 2, 2021
GOP Governor DeSantis Takes A Stand, Bans ‘Vaccine Passport’ via Executive Order
The following article, GOP Governor DeSantis Takes A Stand, Bans ‘Vaccine Passport’ via Executive Order, was first published on Flag…
Read More » -
Great American RepublicApril 2, 2021
Trump Releases ‘Happy Easter’ Statement, Slams ‘Fake News Media’ Over ‘Election Fraud’
The following article, Trump Releases ‘Happy Easter’ Statement, Slams ‘Fake News Media’ Over ‘Election Fraud’, was first published on Flag…
Read More » -
Great American RepublicApril 2, 2021
Baseball Caves to ‘Woke’ Cancel Culture Crowd, Will Move All-Star Game Out of Atlanta
The following article, Baseball Caves to ‘Woke’ Cancel Culture Crowd, Will Move All-Star Game Out of Atlanta, was first published…
Read More » -
Great American RepublicApril 2, 2021
Hunter Biden Admits Laptop ‘Could Be’ His, But MSM Said It Was GOP Smear Campaign
The following article, Hunter Biden Admits Laptop ‘Could Be’ His, But MSM Said It Was GOP Smear Campaign, was first…
Read More » -
Great American RepublicApril 2, 2021
Capitol Building Killer Is Nation of Islam Follower, But Asian Doctor Says It Is Trump’s Fault
The following article, Capitol Building Killer Is Nation of Islam Follower, But Asian Doctor Says It Is Trump’s Fault, was…
Read More » -
Great American RepublicApril 2, 2021
Joe Biden Set to Seriously Look Into Canceling Student Debt (Details)
The following article, Joe Biden Set to Seriously Look Into Canceling Student Debt (Details), was first published on Flag And…
Read More » -
flagandcross
 Great American RepublicApril 2, 2021
Great American RepublicApril 2, 2021Flashback: Biden Says Drunk Driving Not A Felony for Undocumented, Won’t Deport For It
The following article, Flashback: Biden Says Drunk Driving Not A Felony for Undocumented, Won’t Deport For It, was first published…
Read More » -
Great American RepublicApril 2, 2021
ICYMI: Migrant Kids Getting In-Person Schooling In San Diego, US Students Stuck Online
The following article, ICYMI: Migrant Kids Getting In-Person Schooling In San Diego, US Students Stuck Online, was first published on…
Read More » -
Great American RepublicApril 2, 2021
‘Last Thing the Economy Needs Right Now’ – McConnell Responds to Joe’s Historic Tax Proposal
The following article, ‘Last Thing the Economy Needs Right Now’ – McConnell Responds to Joe’s Historic Tax Proposal, was first…
Read More » -
Great American RepublicApril 2, 2021
Report: COVID-19 Is On the Rise Once Again
The following article, Report: COVID-19 Is On the Rise Once Again, was first published on Flag And Cross. Here we…
Read More » -
Great American RepublicApril 2, 2021
Biden Makes Baseball’s Opening Day Political, Calls on MLB to Cancel Atlanta All-Star Game
The following article, Biden Makes Baseball’s Opening Day Political, Calls on MLB to Cancel Atlanta All-Star Game, was first published…
Read More » -
Great American RepublicApril 2, 2021
Cancel Culture Falsely Attacks Voter ID Bills | Schaftlein Report
The following article, Cancel Culture Falsely Attacks Voter ID Bills | Schaftlein Report, was first published on Flag And Cross.…
Read More » -
Great American RepublicApril 2, 2021
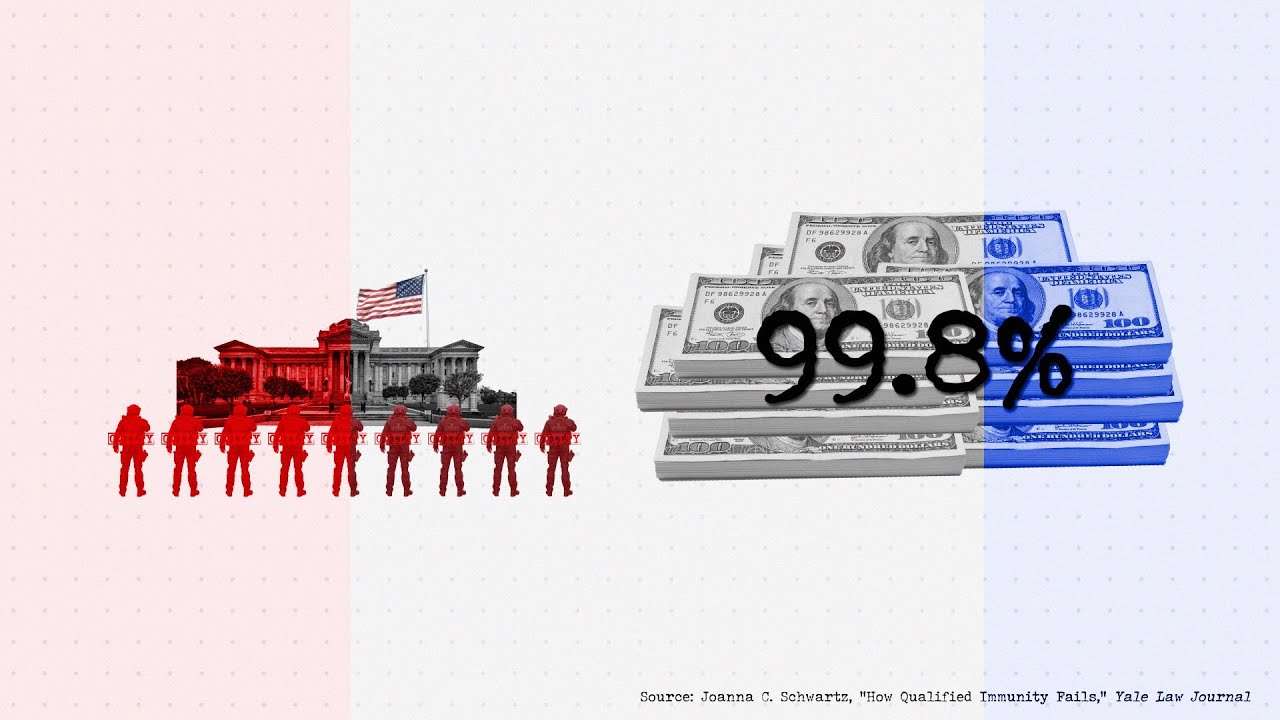
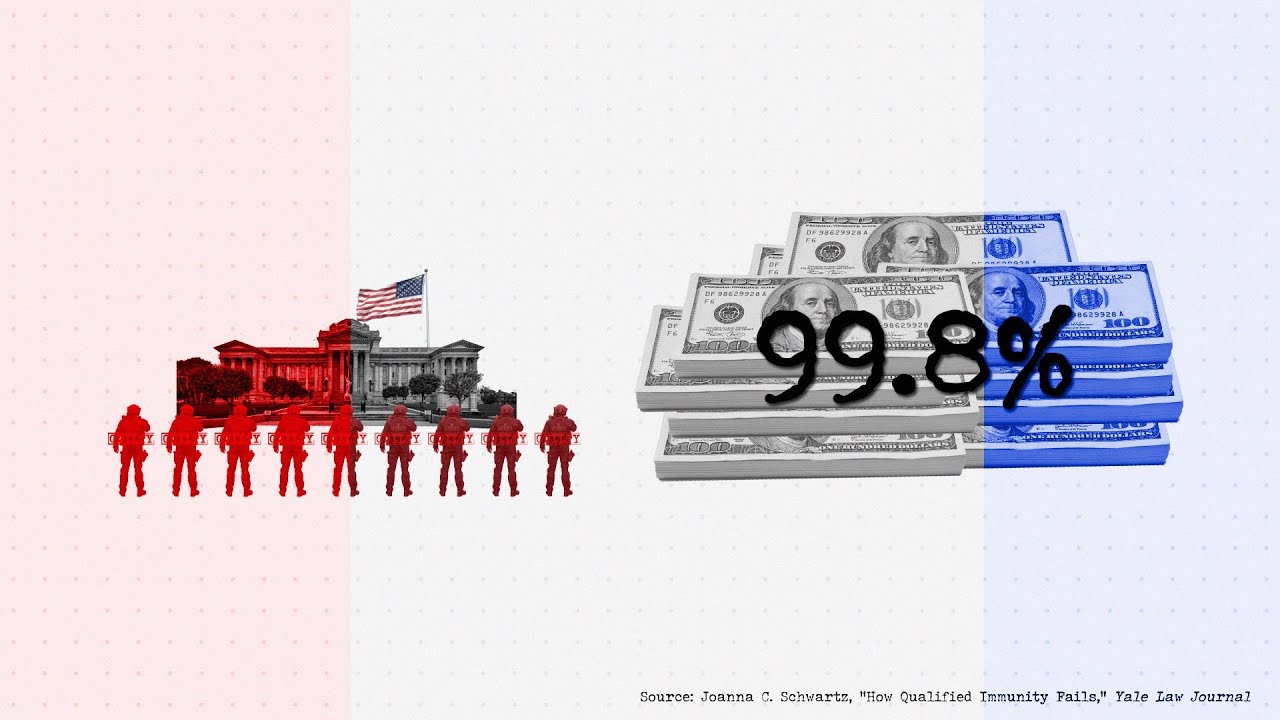
Flashback: Black Lives Matter Wants Biden to Begin ‘Roadmap’ Toward Abolishing Prisons, Cops
The following article, Flashback: Black Lives Matter Wants Biden to Begin ‘Roadmap’ Toward Abolishing Prisons, Cops, was first published on…
Read More » -
Great American RepublicApril 2, 2021
ICYMI: Team Biden Developing Covid Passport for People to Show Proof of Vaccination
The following article, ICYMI: Team Biden Developing Covid Passport for People to Show Proof of Vaccination, was first published on…
Read More » -
flagandcross
 Great American RepublicApril 2, 2021
Great American RepublicApril 2, 2021VIDEO: Ben Shapiro Slams Joe Biden for Ruining Sports, Rips Jill Biden for Spanish Flub
The following article, VIDEO: Ben Shapiro Slams Joe Biden for Ruining Sports, Rips Jill Biden for Spanish Flub, was first…
Read More » -
flagandcross
 Great American RepublicApril 1, 2021
Great American RepublicApril 1, 2021‘Cruel & Heartless Attack on the American Dream’ – Trump Rips Joe for Demanding Tax Hike
The following article, ‘Cruel & Heartless Attack on the American Dream’ – Trump Rips Joe for Demanding Tax Hike, was…
Read More » -
flagandcross
 Great American RepublicApril 1, 2021
Great American RepublicApril 1, 2021‘Cruel & Heartless Attack on the American Dream’ – Trump Rips Joe for Demanding Tax Hike
The following article, ‘Cruel & Heartless Attack on the American Dream’ – Trump Rips Joe for Demanding Tax Hike, was…
Read More » -
Great American RepublicApril 1, 2021
GOP-Controlled Arizona Senate Hires Auditor to Review Maricopa County Election Results
The following article, GOP-Controlled Arizona Senate Hires Auditor to Review Maricopa County Election Results, was first published on Flag And…
Read More » -
Great American RepublicApril 1, 2021
GOP-Controlled Arizona Senate Hires Auditor to Review Maricopa County Election Results
The following article, GOP-Controlled Arizona Senate Hires Auditor to Review Maricopa County Election Results, was first published on Flag And…
Read More »